Phishing is one of the biggest cyber security threats your business faces. Malicious emails are sent from seemingly credible sources to steal sensitive information. This is normally in the form of login details or sensitive information, but can be used to deliver malware.
Sophisticated social engineering is used to make the recipient think the email they have received is genuine.
What is social engineering?
Social engineering is defined as “the use of deception to manipulate individuals into divulging confidential or personal information that may be used for fraudulent purposes.”
This type of fraud has become more popular as it is easier to manipulate you or your staff into giving access or information than it is to hack into the software. Rather than trying to find vulnerabilities in software in systems, a hacker might phone or email a member of staff pretending to be a colleague or third party support team to try and trick them into giving away valuable information.
Social engineering impact on business
Social engineering has a major impact on businesses. In the UK, one small business is successfully hacked every 19 seconds, with around 1.6 million small businesses hacked every year.
Around half of cyber attacks in the UK involve some form of phishing. Its around 20% higher than the global average. Approximately one in every 3,722 emails in the UK is a phishing attempt, and about 55% of all emails in the UK are spam.
Despite increases in phishing and attacks, many businesses and their staff aren’t properly prepared to deal with social engineering and phishing attacks.
Types of Social Engineering Attacks
Phishing
A phishing email aims to trick the target into revealing sensitive information or taking an action that then compromises security.
Spear Phishing
A more targeted form of phishing. Spear phishing emails are more tailored to a specific organisation than a regular phishing email. Spear phishing emails are more likely to be believable, as more effort and research will have been put in.
Baiting
A common form of baiting is to offer free music downloads (or other forms of media). The aim is to get the target to click on the link and enter their login details.
Scareware
This involves victims being bombarded with false alarms and fictitious threats. Users are deceived to think their system is infected with malware, prompting them to install software that has no real benefit (other than for the perpetrator) or is malware itself.
Pretexting
This is where the attacker creates a believable pretext or scenario in which to trick the target into giving them information or even direct access to their systems.
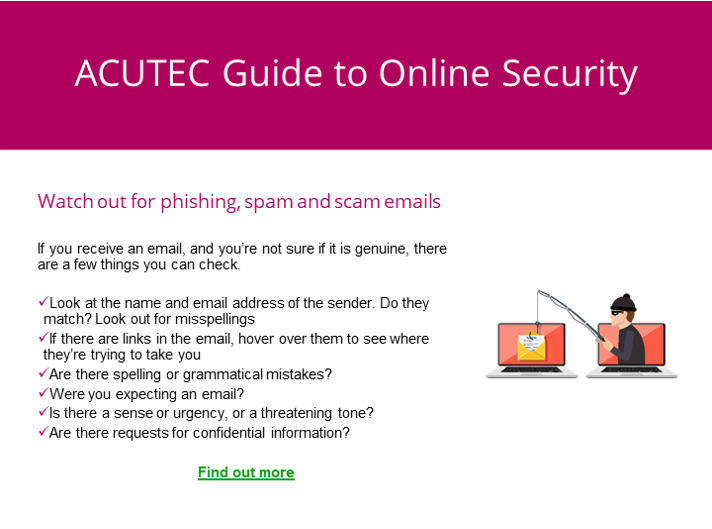
Spotting a Phishing Email
Click the image below to see our online security infographic, particularly our advice for how to spot a phishing email and make sure you don’t fall victim:
If you want to make sure your staff are fully prepared to spot and deal with social engineering, get in touch with ACUTEC today.