Phishing is where you receive an email from what appears to be a trusted source asking you for sensitive information, to open an attachment or click on a link.
But in reality, these emails are not from the believed source and are dangerous. They will use your data against you or infect your computer with malware. Employees within organisations are becoming the weak spots in security because they are unable to spot when they are sent a fraudulent email.
Phishing scams have been around for as long as the internet, and have been considered a serious threat for close to two decades. However, the techniques that scammers use are constantly changing. It’s important, both on the individual and the company level, to stay up-to-date with new phishing scams and techniques that cybercriminals use to commit their crimes.
Since the first phishing scams were launched online, this kind of scam has been all about volume. Phishing scammers focus on targeting large numbers of people—the idea being that while only a small proportion of people fall for the scam, the volume of attempts made ensured that enough people were taken in to make the scam worthwhile.
Phishing Scams to Watch Out For
The core of any phishing scam is an attempt to get the target to give out personal information such as bank account information, account login details, or credit card numbers. Historically, phishing scams have usually been initiated via email. However, as users have become more cautious about their email habits, scammers are starting to target people in other online locations. Email is no longer the only point of vulnerability.
Corporate credentials attacks
Webmail and software products, including Microsoft and Google products, are top of the list of phishing scam targets. If a scammer can obtain the Microsoft login data of just one employee, they can potentially gain access to the files and data of an entire organization.
For this reason, email-based corporate credential phishing attacks are rapidly becoming commonplace. These are phishing attacks that involve the use of fake or compromised login pages. In the corporate world, common targets include Office 365, OneDrive, and LinkedIn login pages.
Spear phishing
Like the name suggests, this kind of phishing is a much more specific kind of operation, in comparison to email-based phishing. Spear phishing is about selecting a single target—either an individual or a company—and focusing efforts on compromising that target. To do this, they tailor email messages, for instance by impersonating an employee, to trick the target recipient into handing over sensitive information.
Current events-related scams
Scams that are based on current events. For instance, when GDPR was enacted, scammers posed as legitimate businesses, requesting sensitive corporate information, claiming it was needed to ensure the company was compliant.
New apps equal new targets
The increasing popularity of messaging apps such as Facebook Messenger, Slack, and WhatsApp have given phishing scammers new locations for finding and targeting their victims. Many users mistakenly think of messaging apps as safe from scammers, but nothing is further from the truth. These messaging apps have very little in the way of security measures, so it’s important for users to be cautious in how they use them.
Examples of Phishing Emails
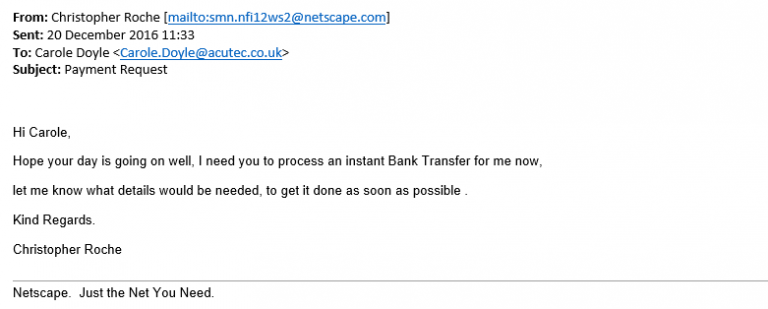
Instant Bank Transfers
Our first example is a targeted phishing email, a spear phishing email. For a little background information, Carole works in ACUTEC’s Finance office and Chris Roche is ACUTEC’s Managing Director. We don’t mind telling you this because it’s easy to find on Google so we’re not making ourselves vulnerable by revealing that information. In this instance, Carole has received an email from what seems to be Chris asking her to make a bank transfer. There are several things wrong with this email. The first is that it says Christopher. Anyone who receives emails from Mr Roche knows that he is Chris, not Christopher. The second is the email address that the message has come from smn.nfi12ws2@netscape.com is not Chris’s email address.
The other thing to look out for with a phishing email is the tone. If it seems odd you should question it. Carole would question this email because there is no context and it’s not how Chris would normally communicate. He would never send ‘kind regards’ in an internal email.
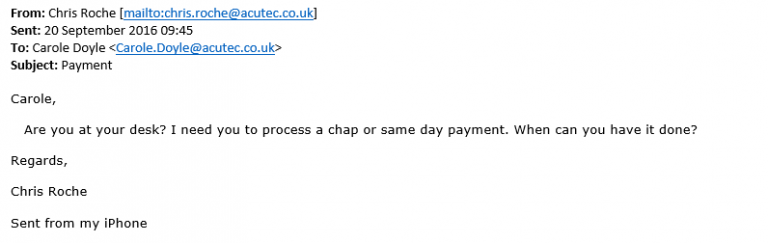
Payment Request
The below email is similar in ways to the first, although there are differences. In this case the correct name and email address are being used so it’s less easy to spot. In this case, you would need to be very aware of the tone and context of the email and review whether it seems strange to you. The giveaway in this email for Carole was the ‘Sent from my iPhone’ as Chris prefers Android phones.
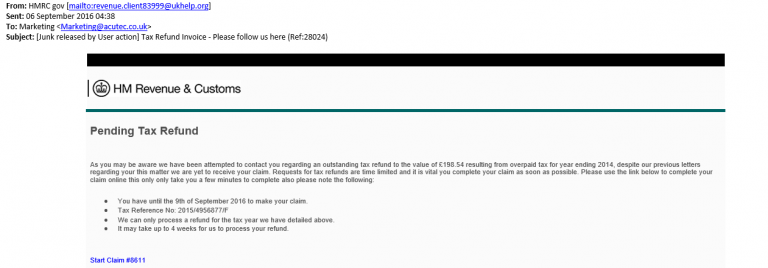
HM Revenue & Customs
The below screenshot is of a less targeted phishing campaign. It’s not pretending to be someone you know but it is pretending to be a trusted source, in this case HM Revenue & Customs. The format appears the same as a genuine email. Again, the source of the email address does not seem genuine in this case and if you hover your mouse over the link in the original email you can see it would take you to an unfamiliar website.
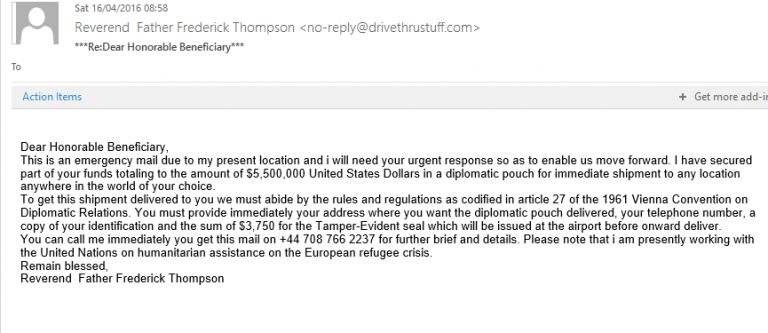
Inheritance Scams
Some emails you will just immediately junk without it even registering that they are a phishing email. In the below email the individual has stated that you are the beneficiary of a considerable sum of money. For you to gain this money you will need to provide personal information and a smaller sum to gain access, obviously there is no bountiful inheritance waiting for you when you pay.
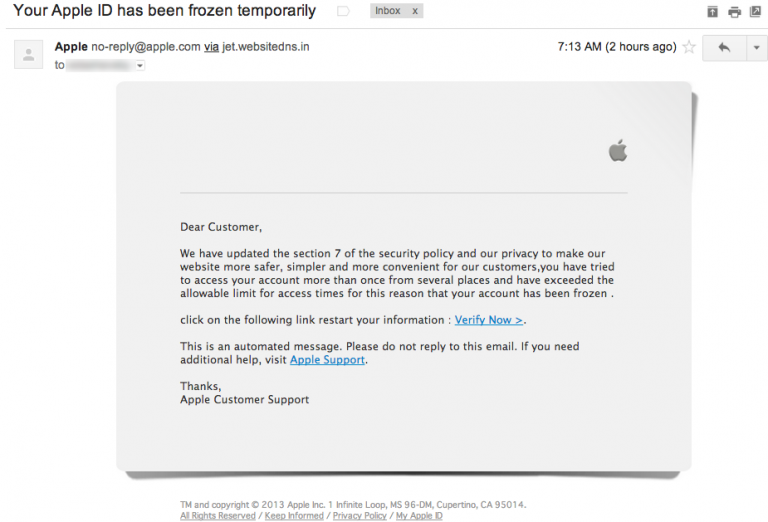
Apple
We have received a few emails masquerading as Apple. In the case below it says that the Apple ID has been frozen and information needs verifying. You need to think when you receive an email like this from certain providers. Is your work email address linked to an Apple account? Is it linked to Amazon? If not then the likelihood is that you have received a fraudulent email and you can just hit delete straight away.
How to Spot Phishing Emails
The internet, the technology driving it, and the people who use it, are all far more sophisticated than ever before. But so are the cybercriminals who develop and launch phishing scams online. It’s harder to stay safe online these days and spot phishing emails, as internet users must do more than ignore suspicious-looking emails. The following measures can help employees avoid being taken in, keeping both themselves and the organization safe.
Private information requests
Any email that requests private information should be viewed with caution, especially if the email is marked “urgent” or otherwise asks the recipient to act quickly. These emails use a sense of urgency to induce the recipient to take action without thinking critically about the email.
Instead of providing the information immediately, contact the relevant company directly and find out if the request is genuine.
Download links and requests
Both emails and websites can contain malicious download links that purport to contain important information. Malicious download links typically contain malware of some kind; for instance, viruses that record keystrokes—allowing a scammer to steal sensitive information such as credit card or bank account numbers.
Whether it’s within an email or on a website, users should not download anything unless they’re confident that it’s safe. If in doubt, don’t click the download link.
Email harvesting scams
Some scams “harvest” email addresses using bots that scan websites looking for text that uses the classic email format of name@server.com. Avoid this scam by writing email addresses as name [at] server [dot] com or something similar. People can read and understand it, but bots won’t recognize it as an email address.
It’s also important to be cautious about providing email addresses when they’re requested, for instance in email subscription boxes or credentials requests. Don’t provide email addresses if you’re in any way unsure about the origins of the request.
Be wary of messaging apps
Messaging apps are increasingly targeted by scammers, so it’s important to be just as cautious with instant messages as you are with emails. Download links should be treated with care, especially if they’re unsolicited. And, any download links that come from unknown senders should be avoided.
No Signature
If the person who has emailed you usually has a signature and it’s not there this is a warning sign as the email has not come from its usual source. Contact the person in a different way such as a phone call, text or even face to face if they are in your office and make sure before you reply.
Spelling Mistakes
Spelling mistakes are usually a big giveaway on phishing emails. If an email from Lloyds Bank is riddled with spelling mistakes you can bet that it’s probably not Lloyds Bank that has sent it to you.
Mismatched URLs
Phishing emails often contain links. If you hover over the link it will show you the actual hyperlinked address. If the two don’t match it’s suspicious and we wouldn’t recommend clicking on the link.
Misleading Domain Names
The email may say that it has come from John Smith but does the actual email address match up with that? We have seen both phishing and spear phishing emails with domain names in the email address that are quite obviously not legitimate. Transactionsafetypost@mail.com is quite obviously not PayPal’s email address.
It’s Irrelevant
You’re unlikely to register for an Apple or Amazon account to your work email unless its part of your job to use their services, so if you receive an email at work from them then you should be suspicious. It’s the same as when you’re told you have won the lottery but you haven’t bought a ticket. You haven’t initiated any interaction with that organisation so there is no reason for them to contact you.
Don’t get caught out by phishing emails. If you’re worried about your business is vulnerable to phishing, get in touch with ACUTEC today, and we can help to prepare your team.